Secure Data Destruction Methods: A Comprehensive Guide
In today's digital age, businesses can no longer afford to overlook the importance of secure data destruction. With the risk of data breaches and cyber attacks constantly looming, having a reliable and effective data destruction method in place is crucial. In this article, we'll explore the top secure data destruction methods, the most common types of data destruction, and provide you with tips to choose the best method for your business needs.
Why is Secure Data Destruction Important?
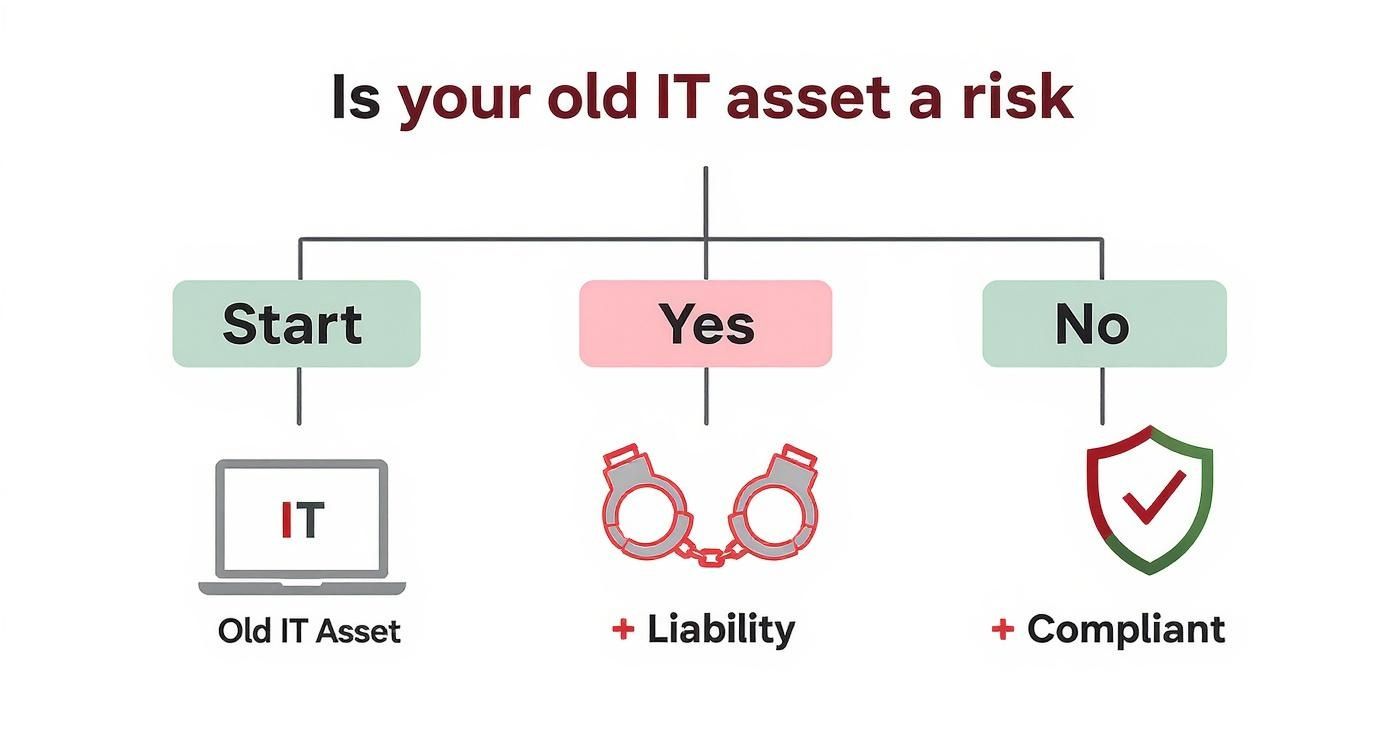
Data destruction is the process of permanently eliminating data from storage devices to prevent unauthorized access, data breaches, or cyber attacks. This is especially crucial for businesses that handle sensitive information, such as financial data, medical records, or personal identifiable information (PII). With the increasing number of data breaches and cyber attacks, having a secure data destruction method in place can help prevent financial losses, reputational damage, and legal exposure.
Types of Data Destruction Methods
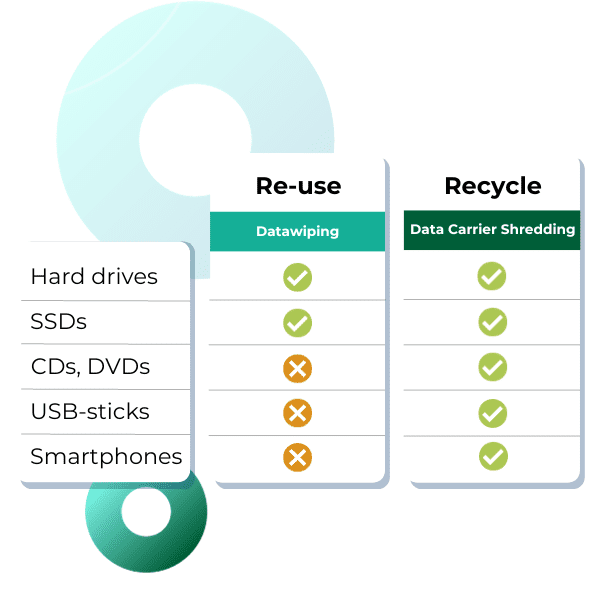
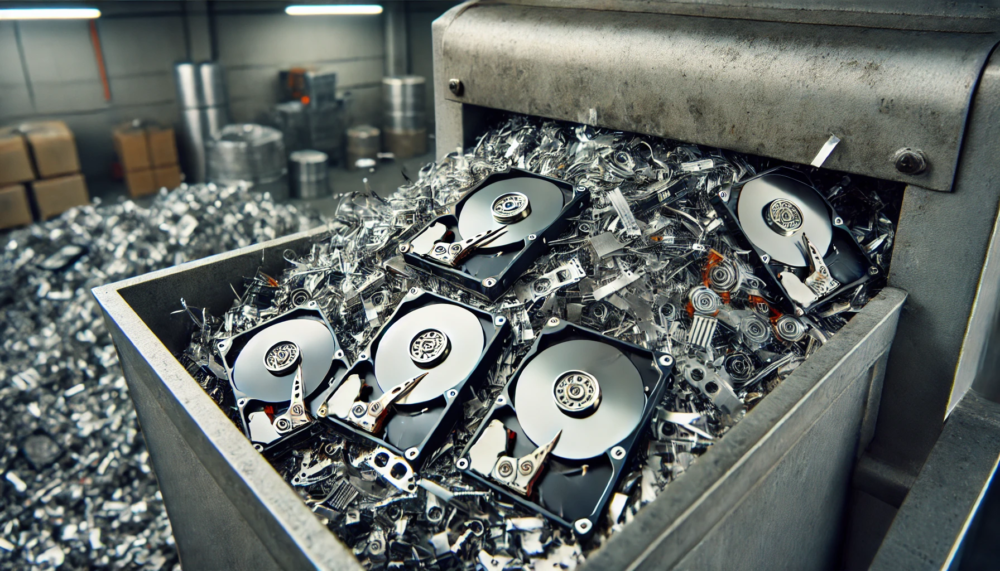
- Physical Destruction: This method involves physically destroying the storage device, such as hard drives, solid-state drives, or USB drives, using a physical degradation method, such as crushing, shredding, or incineration.
- Logical Destruction: This method involves deleting data using software or firmware, ensuring that the data is unrecoverable using current technological means.
- Degaussing: This method involves using a degaussing device to erase data stored on magnetic media, such as hard drives or magnetic tapes, by demagnetizing the storage surfaces.
- Data Wiping: This method involves overwriting data on storage devices multiple times to make it unrecoverable, using methods such as DoD 5220.22-M or BSI-7236.
- Blockchain-based Data Destruction: This method uses blockchain technology to securely and irreversibly delete data, making it virtually impossible to recover.
Choosing the Right Data Destruction Method
The choice of data destruction method depends on various factors, including the type of data being destroyed, the condition of the storage device, and the required level of security. Here are some factors to consider when choosing a data destruction method:
- Data Type: Choose a method that is suitable for the type of data being destroyed, such as sensitive financial data or personal identifiable information.
- Storage Device Condition: Consider the condition of the storage device and choose a method that can handle devices in various states of wear and tear.
- Security Requirements: Choose a method that meets or exceeds the required security standards for your industry or organization.
- Cost: Consider the cost of the data destruction method, including the cost of equipment, labor, and disposal.
- Regulatory Compliance: Ensure that your chosen data destruction method complies with relevant regulations and industry standards.

Best Practices for Secure Data Destruction
To ensure secure data destruction, follow these best practices:
- Develop a Data Destruction Policy: Establish a clear data destruction policy that outlines the procedures for handling and destroying business data.
- Identify and Destroy Sensitive Data: Regularly identify and destroy sensitive data, including financial data, personal identifiable information, and confidential business information.
- Use Secure Methods: Choose a secure data destruction method that meets or exceeds the required security standards for your industry or organization.
- Document the Process: Keep records of the data destruction process, including the methods used, dates, and times.
Conclusion
Secure data destruction is a critical component of any business's data security strategy. By understanding the types of data destruction methods available, choosing the right method for your business needs, and following best practices for secure data destruction, you can protect your business from data breaches, cyber attacks, and reputational damage. Remember to stay up-to-date with regulatory changes and adapt your data destruction policies accordingly to ensure continuous compliance and protection of your business data.
Additional Resources
For more information on secure data destruction methods and best practices, check out the following resources:
- NAID AAA Certification: The National Association for Information Destruction (NAID) AAA certification ensures that data destruction vendors meet strict standards for secure data destruction.
- DoD 5220.22-M: This standard provides guidelines for deleting data on digital devices to ensure that it is unrecoverable.
- BSI/VSITR: This standard provides guidelines for secure data destruction in the European Union.






![Secure IT Asset Disposal [ITAD] & Data Destruction Services Secure IT Asset Disposal [ITAD] & Data Destruction Services](https://total-shred.com/wp-content/uploads/2024/10/Choosing-a-Reliable-Data-Destruction-Service-1024x771.jpg)